We are Passionate
We deliver unforgettable vacations to guests who trust us with life’s greatest moments
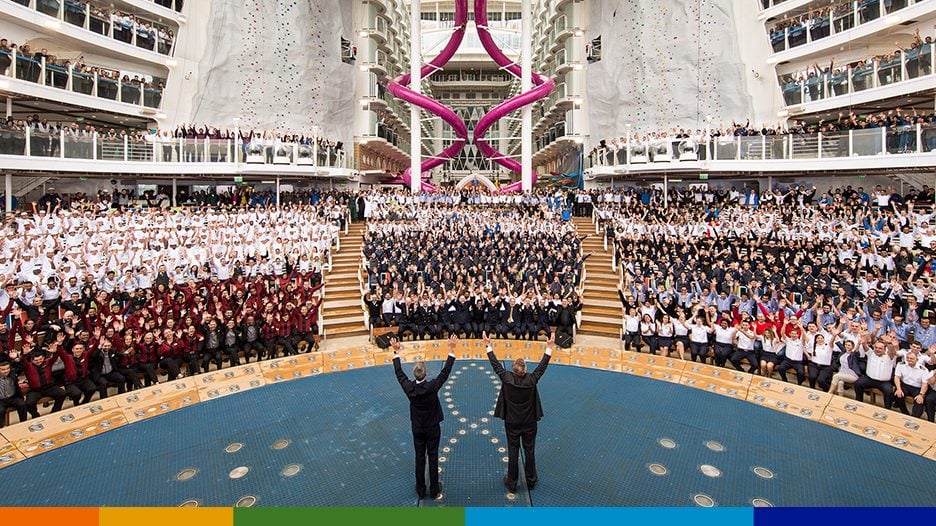
Discover why our crew is the reason our guests keep coming back for more.


Discover why our crew is the reason our guests keep coming back for more.


We are elevated by technology and are always looking beyond the horizon.


We open the world to our employees. We travel most of the known world, and our crew is there every step of the way.


They are the heart of our organization. They are the ones that propel us forward.
Learn more